Recently we completed a project for a large not-for-profit client who has circa 50 x offices and over 350 staff, many working in highly-regulated and/or secure environments where gaining remote access to corporate services has been notoriously difficult.
Our client initially was inving a Direct Access solution, however, after discussion with Carbon around Microsoft’s roadmap, we collectively decided to implement AlwaysOnVPN as this is where Microsoft’s efforts are focused moving forward, particularly in conjunction with Windows 10.
The Solution:-
Microsoft Surface Pro
Windows 10
Microsoft Windows Server 2016
Office 365
Azure AD Premium
Intune
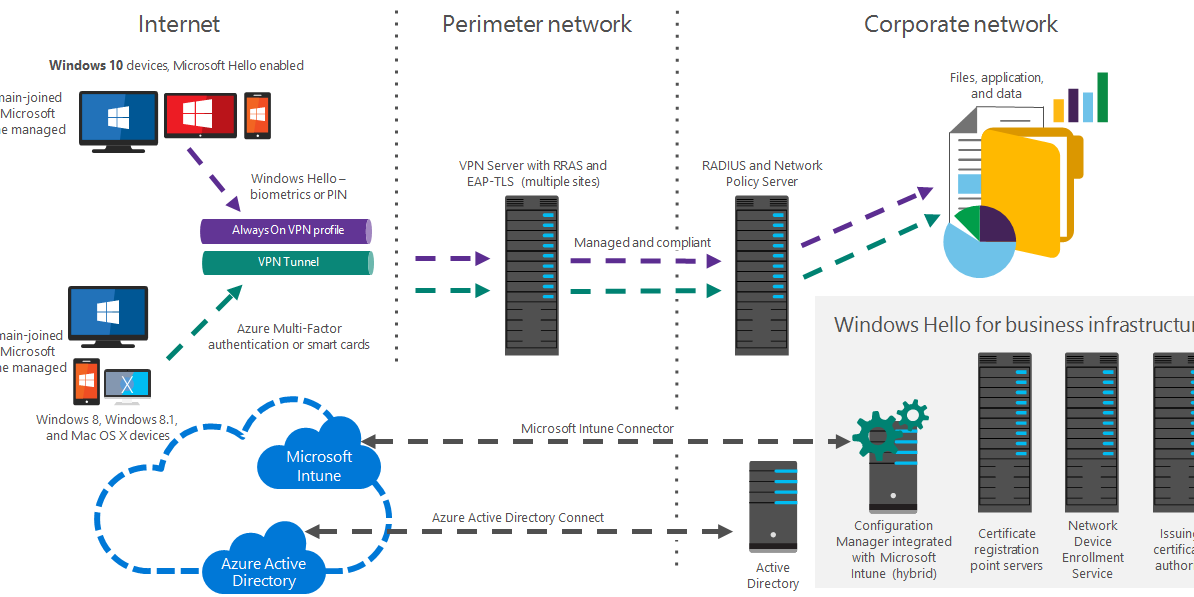
Initially, we setup the back-end infrastructure, validating the current Azure AD vs On-Prem environment and ensuring that Intune has been configured as the primary MDM provider. This allows the client to domain-join the client and deploy the AlwaysOnVPNconfiguration (Powershell/XML) to the Surface P3ro devices via GPO to establish a (pre-logon) device tunnel. Auto-enrollment for Intune/MDM is configured so that domain-joined devices are automatically provisioned and allocated in Azure AD/Intune.
Deployment of WPAD/Proxy Auto Configuration allows forcing certain traffic through the Corporate network in order to use the existing Web Proxy for filtering and advanced routing to ensure certain SaaS applications are only accessed via secure links. Inside the corporate network (or in a remote office), connections are made via site-to-site VPN’s on site routers. Outside of the corporate network, devices still tunnel all internet communications via the corporate Web Proxy/AlwaysOnVPN tunnel as part of a Force Tunnel configuration.
Now that all the devices can be managed via GPO/Intune, additional items can be pushed out to clients, including in this case, Bitlocker utilising the TPM capabilities of the new Surface Pro hardware.
In summary, we have achieved the project deliverables using new, advanced Microsoft technology and a more future-proof option than Direct Access, with full AzureAD Integration. There are quite a few “gotchas” with AlwaysOnVPN and Microsoft are continually developing and improving (unfortunately documentation is not quite there yet!) so if this is a technology that you are looking at, either to replace existing legacy VPN or Direct Access then let us know and we’ll be happy to advise.
More Information from Microsoft on AlwaysOnVPN can be found here.